Learn how to avoid a cyber-attack on your small business and how to respond to ransom threats.
 The email from Amazon may look completely legitimate. It includes the same Amazon writing and gold smiley face arrow. It says it’s from the Amazon billing department, which may seem logical after recent purchases.
The email from Amazon may look completely legitimate. It includes the same Amazon writing and gold smiley face arrow. It says it’s from the Amazon billing department, which may seem logical after recent purchases.
Upon closer inspection, the sender is not an Amazon.com email address, the domain is inaccurate, and the content of the message has grammatical and spelling errors.
These are all things business owners need to watch for, cybersecurity experts say. Small-business owners are most often the easiest victims when it comes to hackers, ransomware and other cybersecurity threats, experts and data show.
Almost half of small businesses have suffered a cyberattack in the past year. This is mostly because small businesses are less likely to have protections in place to prevent an attack or to detect one when it happens. As a result, small businesses are less likely to be able to financially recover from a breach or hack, according to the 2018 Small Business Security Report, conducted for Hiscox, a U.S. insurance company that provides cybersecurity insurance to small businesses.
Experts say cybersecurity is a multi-level approach that involves three main areas: prevention, detection and mitigation. Here are six questions to ask when considering whether your small business is cyber secure:
1. What dangers exist?

Multiple types of cyberattacks can happen, but the most common one is ransomware, which is a hack that locks the owner of the data out of its information and demands payment or a “ransom” for its release.
A ransomware attack can take one of two forms:
• The hacker preys on a specific organization and demands a large ransom for the release of files.
• The hacker casts a wider net to seek more modest payments. This is where small businesses often fall prey.
Ransomware is becoming more sophisticated: Nine out of 10 phishing emails are now ransomware. About 75 million phishing scam emails are sent every day, and more than 40,000 cyberattacks occur each day, according to information provided by All Covered, IT Services from Konica Minolta in Urbandale.
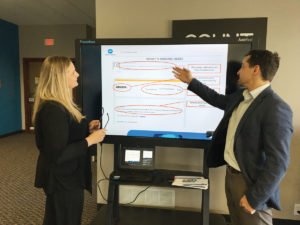
More than 90 percent of cyberattacks begin with a spear phishing email similar to the ones Garrett Christeson, a senior information technology consultant for All Covered, IT Services, showed Urbandale Chamber of Commerce President Tiffany Menke from a faux-Amazon sender.
2. Is a threat likely to occur?
As long as a company has employees, the answer is likely yes.
“Employees are usually the weakest link,” says Ryan Weston, the manager of security and connectivity for Associated Computer Systems Ltd. in Urbandale.
Most ransomware attacks happen as a result of an employee clicking on a link in an email or opening an email attachment that was an attack.
Cyberattacks are becoming more common as hackers get smarter. No system is 100 percent secure even with the most diligent security professionals attempting to provide protection against every threat, Christeson says.
According to Hiscox’s report, which is based on claims data, 47 percent of small businesses suffered a cyberattack. Forty-four percent had between two and four attacks.
The issue happens frequently, local technology advisers say, but it is rarely reported to local law enforcement, according to calls to local police and sheriff’s departments, unless it is a large-scale attack or an attack on a well known company or entity.
In October 2017, a hacker group was believed to have stolen student data from Johnston Community Schools that included names, addresses and telephone numbers and posted them to a publicly accessible website. Some parents reported they received messages that allegedly threatened their children as a result of the hack.
Laura Sprague, the communications director for the district, says specific district policies were not changed as a result of the cyberattack, but officials changed Johnston’s relationship with third-party vendors.
In light of the incident, officials contracted with a cybersecurity technology company to conduct an audit, which revealed that hackers had not reached the district’s server, and that there was no internal breach. The audit
revealed that a cloud site used by one of the district’s third-party vendors was part of the hack, which is how Johnston’s student data had been stolen.
As a result, Johnston officials have worked with Iowa’s Chief Information Officer and the cybersecurity technology
company, CrowdStrike, to implement a new threat prevention platform that includes an intrusion detection system. The state’s Security Operations Center now monitors Johnston’s network from the center.
District officials require all of their thirdparty vendors to now enter into a nondisclosure agreement. Each vendor also was required to submit written documentation to prove that any student data it shared with other vendors
was secure. As a result, some of the district’s vendors ended their relationships with other vendors that could not guarantee security of data, Sprague says.
The investigation into last year’s cyberattack is still ongoing, she says.
3. How do I thwart a would-be cyberattack?
Take preventative action, information technology managed services experts say.
This includes the tools and solutions to prevent infections and detect weaknesses in the network’s security. Education at all levels of the business about cyber threats also is paramount.
“The best defense is a good offense, and end-users understanding where breaches come from and how they can play a big part in prevention is critical to a security plan,” Christeson says.
Business owners should treat cybersecurity as a line item in their budget process to ensure it receives proper attention. All employees should receive cybersecurity training as part of their onboarding process and through routine trainings.
Even though the warnings are there, business owners often don’t make changes — even after an attack — or take precautions. According to Hiscox’s report, 50 percent say it’s because they don’t have enough money in
their budget to pay for cybersecurity services.
A business with 25 to 50 employees could spend between $1,000 and $1,200 a month for a managed IT services company to provide IT support and training and to serve as the company’s help desk for any issues. Larger companies would likely pay less, Christeson says, because they have their own IT professionals and would only use the external company in the case of more severe IT problems.
Weston recommends businesses utilize training through a managed services provider to show employees what to watch for and then to test them through various modules and a series of phishing emails.
“We can see who clicks on what attachments they shouldn’t have and put them on remedial training,” he says.
Cybersecurity experts recommend a multilevel approach that begins with education of the business’ employees. Even if the company outsources its data protection, the business owner or manager must ensure employees do
their part in house to follow protocols and to keep data secure.
“I think it’s important for people to know and treat the data at the organization or the business like it’s our own,” Christeson says.
He says technology companies, including his own, offer free trainings to business groups for professionals to learn more.
He describes data as the middle of an onion, which is protected by multiple security layers.
Basic layers of cybersecurity include:
• Regular back-ups of the company’s data. Christeson suggests both on site as well as cloud storage.
• Installation of software programs that search for and stop viruses, malware, ransomware and other potential attacks. This includes firewalls and data encryption programs. Christeson suggests using a business-grade product.
• Assurances that all programs have undergone appropriate updates and patches to ensure the most effective version is in operation.
• Protection for the company’s website from hackers.
• Educating employees about the dangers and providing regular tests to ensure they follow procedures.
• Hiring an information technology consultant or managed services provider to oversee and test security procedures.
Christeson suggests business owners take an online survey to determine their risks. One is available through his company at: https://www.allcovered.com/services/it-security/it-quiz.
4. Could my business recover?
Any ransom can be devastating to a business owner because it can disrupt operation, ruin the business’ reputation or brand, and cost thousands to millions of dollars and volumes of employees’ worktime to remedy.
“They really need to take a look in the mirror and say to themselves: ‘What would happen if my data wasn’t here tomorrow?’ ” says Christeson, who mostly works with business with 25 to 500 employees.
Business owners need to consider what it would take to recover from a ransomware attack, which is why a good back-up system needs to be in place, he says.
A business owner needs to consider not only loss of data but the down time the business would experience if data had to be recovered and/or restored, combined with the ransom to get it back, Weston says.
If the data is backed up, the business owner also needs to consider how much time it will take to restore the information. The frequency of a data back-up will depend upon the nature of the business and its tolerance for risk and is something the business owner will need to consider, he says.
“The more frequent, the more expensive the solution,” Weston says.
Small business owners estimated the average cost for cybersecurity incidents in the past year to be about $34,600, according to Hiscox’s claims data. This can escalate into hundreds of thousands of dollars or even
millions for larger companies with more employees. The company also could be held liable for contract violation if any client’s personal data was compromised during a hack.
Depending on the severity of the attack and the data that was compromised, business owners may have to notify customers and publicly explain how they will ensure future attacks do not occur.
“For some of these companies, if it gets out in the public they’ve had a breach, it’s end of story,” Christeson says.
5. What do I do if I have an attack?

Every ransomware attack is different, so it’s important the business owner and their IT services team evaluate it.
Detection is a big component in stopping an attempted ransomware or cyberattack. Both thwarted and successful violations need to be tracked, and alerts need to be put in place that automatically monitor and provide a notification that the network has been attacked.
If a business owner, manager or employee suspects the network could be infected, Christeson advises they do not turn off the machine but instead immediately disconnect the infected computer from any network it is connected to, turn off wireless access, and unplug any USB or external hard drives. He recommends not trying to erase anything or clean up the computer.
Instead, he said to consider the scope of the attack: Was the machine on a shared network when the user first noticed suspicious behavior? Was the operator using any external drives? Is the computer connected to cloud-based storage? Did the user open an email or visit a website?
Then, both Christeson and Weston recommend the business owner contact a trusted managed services provider to evaluate options. They also say: Don’t pay the ransom if one is threatened for return of the data.
“The crazy thing are the hackers holding these companies ransom,” Christeson says.“They aren’t giving their data back at the end of the day.”
Weston agrees and says if the owner has a way to restore the files after receiving a ransom, they should do so and move on. If they don’t and the potential liability is more than $10,000, they need to contact the FBI.
“Typically, they can’t help, but it’s always a good idea to get the cyber attackers under a watchful eye,” he says.
If the business has no way to recreate the data and no back-up — and must have the information — then it will be stuck paying the ransom, Weston says. There’s not guarantee the data will be returned in a usable format, as the files could be locked and unable to be unencrypted. Paying the ransom could also make the business a target for future attacks.
“The more likely they pay it, the more likely (hackers) are to keep sending out ransomware attacks,” Weston says. “If they pay out, they’re on the list to likely pay again. They keep a list of those who pay and those who don’t, and those who pay keep getting hit over and over again.”
Christeson says an IT services provider can help the business owner determine if data can be restored from a recent backup, whether to decrypt files from a third-party decryptor, consider the data a loss, or negotiate/pay the
ransom as a last resort.
6. What future steps do I need to take?
IT experts say business owners need to act to ensure future attacks do not occur. This includes a plan for how to handle all incidents, from detection of an attack and containment to notification of appropriate individuals and assessment. Each person who will be involved needs to be notified of his or her specific roles and responsibilities prior to any incident. Response plans need to be regularly updated to account for new types of threats.
Don’t “Set it and forget it,” Christeson says. “It needs to be regularly reviewed, measured for effectiveness and modified if/when needed. Strong security governance and oversight are critical.”
According to Hiscox’s report, about 65 percent of small-business owners failed to act following a cybersecurity incident, and only 16 percent of the small businesses surveyed were very confident in their cybersecurity readiness.
Most did not have a strategy for cybersecurity readiness or anyone charged with overseeing the area or outsourcing the service. Less than one third of businesses conducted phishing experiments to check employees’ behavior and readiness to thwart any future attacks.
Christeson works with clients to conduct vulnerability and penetration testing to determine where there are weaknesses in the network’s security system. He utilizes a third-party provider to then try to hack into the system to show a company just how far a hacker can get into the network.
Experts also recommend business owners have a standalone cyber insurance policy to protect the company in case of a cyberattack. The policy is designed to cover privacy, data and network exposures.
“It’s incredibly scary to see how far these good guys can get in and what they can see,” he says. ♦
superbeets review
This is very interesting, You are a very skilled blogger. I have joined your rss feed and look forward to seeking more of your magnificent post. Also, I’ve shared your site in my social networks!|